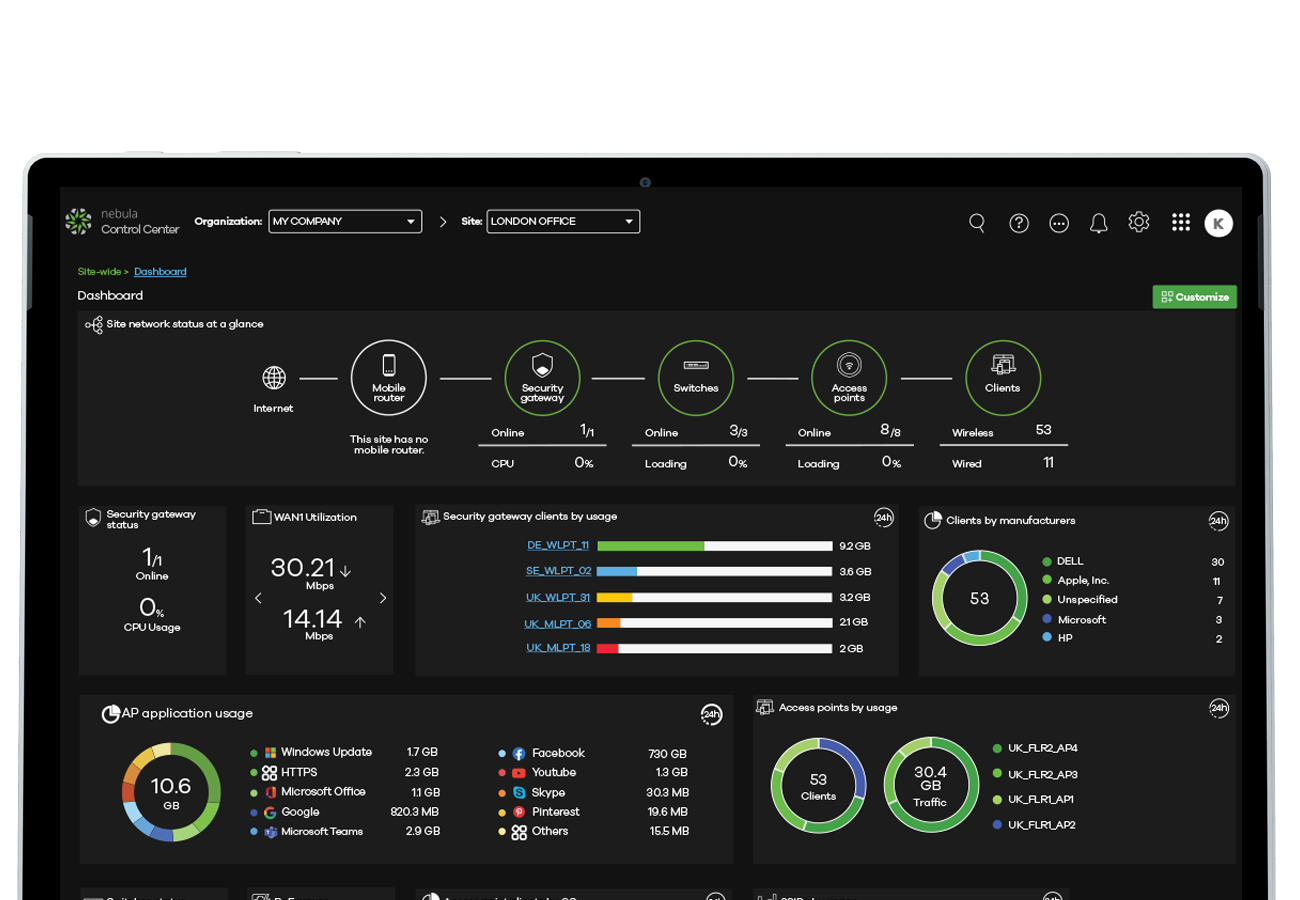
Take the hassle out of connecting remote sites.
Establish L2TP or site-to-site VPNs to keep remote locations securely connected. Site-to-site or hub-and-spoke VPN connections can be configured with complete simplicity through a few simple clicks, without any complex VPN configuration steps.
Get StartedRemote workplaces simplified.
Our new secure WiFi feature allows you to create a 'drop-in' access point (selected models) that can be configured to replicate the SSID of your office and automatically create a secure tunnel, creating seamless accessibility to your corporate network.
Site-to-Site Connectivity.
Site-to-site or hub-and-spoke VPN connections can be configured with complete simplicity through a few simple clicks, without any complex VPN configuration steps.
Remote Native VPN Deployment.
Utilize native in-built VPN client solutions (L2TP) which are supported by the majority of mainstream devices and operating systems. When configured in Nebula you can send auto-deployment scripts to ease the process of remote deployment to end-users.
VPN High Availability (HA).
Advanced VPN technology deploys two IPSec VPN tunnels for active-active VPN load balancing or active-passive failover.
Robust & Secure SHA2 VPN.
High-throughput IPSec, L2TP VPN capabilities, reinforced with advanced SHA-2 encryption.
2FA on Remote Connectivity.
Add an additional layer of protection for both your client devices and your corporate network by applying 2FA to VPN connectivity.
Securing connectivity for remote devices.
Utilize native in-built VPN client solutions (L2TP) which are supported by the majority of mainstream devices and operating systems.
When configured in Nebula, you can send auto-deployment scripts to ease the process of remote deployment to end-users.


Remote workplaces simplified.
Our new secure WiFi feature allows you to create a 'drop-in' access point (selected models) that can be configured to replicate the SSID of your office and automatically create a secure tunnel, creating seamless accessibility to your corporate network.
This simplifies the deployment by creating a plug-and-play option while maintaining a high level of control over the security of remote workplaces.
Never trust, always verify.
In today's environments, the complexity of BYOD, IoT devices and remote working brings an enormous amount of risk for business networks.
A 'never trust, always verify' methodology, also commonly known as 'Zero Trust', is an important step for many businesses.